The Bell-LaPadula Model is a fundamental security framework designed to protect classified information by controlling how data flows within a system. Unlike integrity-focused models, Bell-LaPadula's primary goal is maintaining confidentiality—preventing unauthorized users from accessing sensitive information and stopping authorized users from accidentally leaking it to lower security levels.
This confidentiality model remains one of the most important access control frameworks in cybersecurity. While the Biba Model protects data integrity, Bell-LaPadula protects secrets from unauthorized disclosure. Understanding this distinction is essential for CISSP candidates, particularly in the Security Architecture and Engineering domain where access control models are frequently tested.
Watch the complete explanation of the Bell-LaPadula Model with practical examples and CISSP exam tips.
What is the Bell-LaPadula Model?
The Bell-LaPadula Model is a security framework designed to protect classified information by controlling how data flows within a system. It focuses on one primary goal: maintaining confidentiality. This model prevents unauthorized users from accessing sensitive information and stops authorized users from accidentally leaking it to lower security levels.
Bell-LaPadula is the most famous example of Mandatory Access Control (MAC). In a MAC environment, the operating system constrains the ability of a subject (user) to access or perform operations on an object (file) based on rule-based security labels. Users cannot simply share files at their own discretion (which would be Discretionary Access Control, or DAC).
Core Purpose: Confidentiality Protection
While integrity ensures data remains accurate and unmodified, confidentiality ensures data remains secret from unauthorized viewers. Consider a military intelligence agency where classified documents must be protected from unauthorized access, or a government agency handling sensitive national security information. In these scenarios, unauthorized disclosure could have devastating consequences even if the data itself remained accurate.
Confidentiality ensures data remains secret from unauthorized viewers. Integrity ensures data remains accurate, complete, and unmodified by unauthorized sources. The Bell-LaPadula Model exclusively addresses confidentiality—it has no mechanisms for protecting integrity or availability.
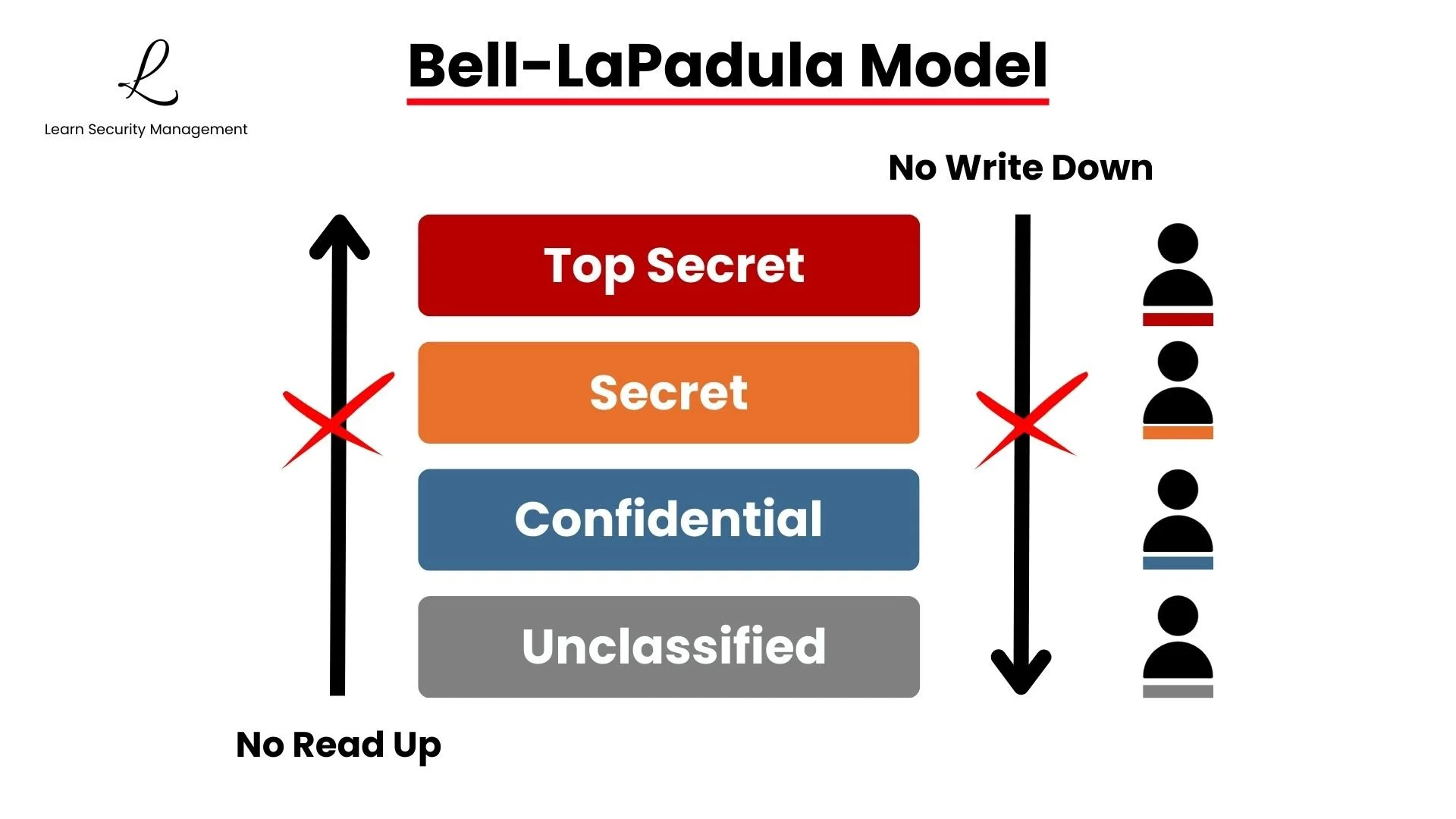
The model operates on a simple premise: information should only flow in directions that preserve secrecy. Classified data should never be exposed to users without proper clearance, and users should never write sensitive information to locations where less-cleared individuals can access it. This controlled flow forms the foundation of the model's two core rules.
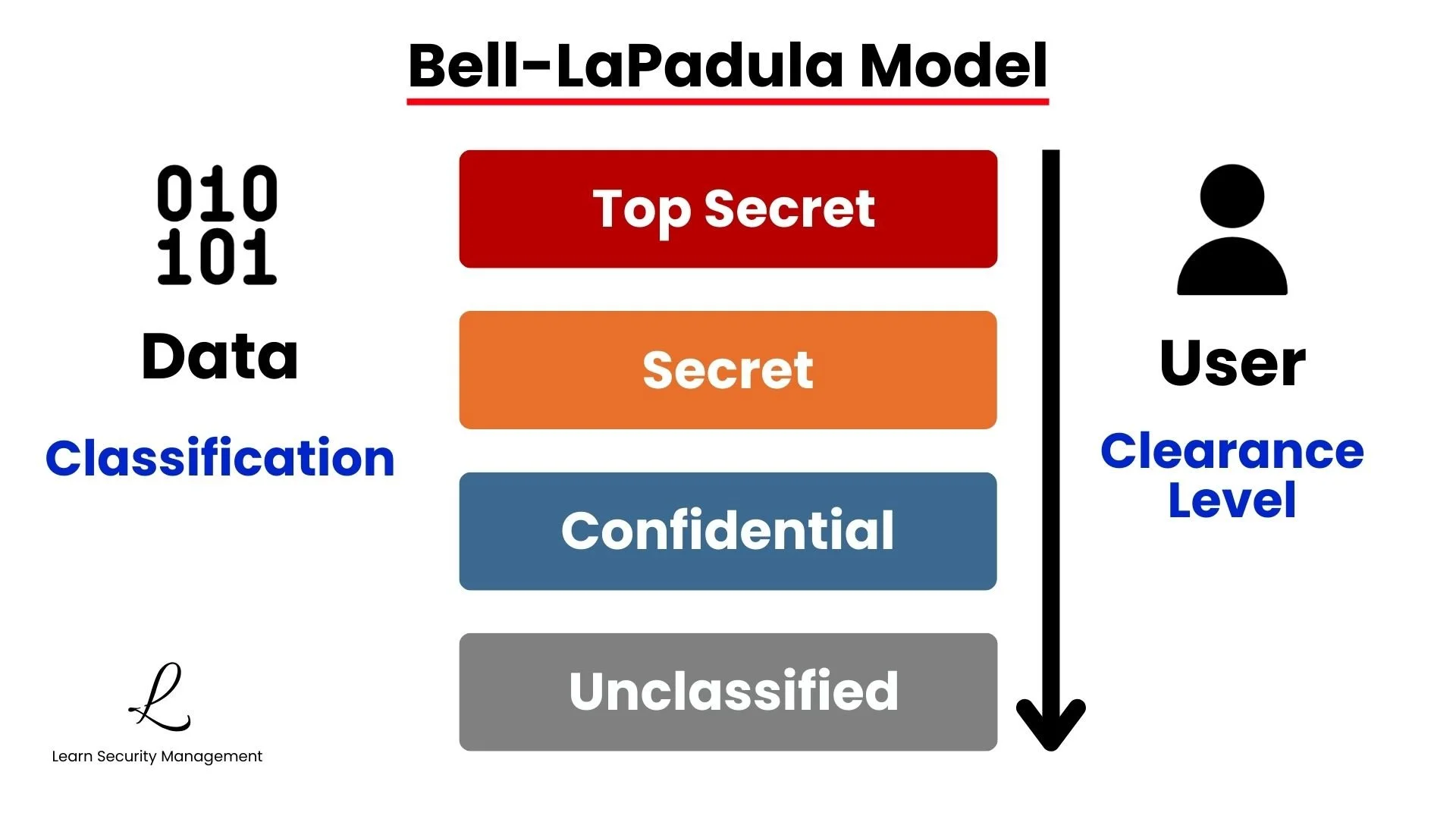
Security Levels and Clearances
Before diving into the rules, it's essential to understand how Bell-LaPadula organizes information and users through security levels. These levels form a hierarchy that determines what data users can access and where they can store information.
The Security Hierarchy
The model assigns every piece of data a classification level and every user a clearance level. These levels form a hierarchy from top to bottom, typically organized as:
| Classification Level | Description | Example Data |
|---|---|---|
| Top Secret | Highest sensitivity, grave national security impact | Intelligence operations, nuclear codes |
| Secret | High sensitivity, serious national security impact | Military plans, diplomatic communications |
| Confidential | Moderate sensitivity, damage to national security | Logistics data, personnel records |
| Unclassified | Public or non-sensitive information | Press releases, public documents |
Your clearance determines the maximum classification level you can access. Think of it like a trust rating—Top Secret clearance means you've been vetted to handle the most sensitive information, while lower clearances limit your access to less sensitive materials.
Security levels reflect the sensitivity of data and the potential damage from unauthorized disclosure, not its accuracy or verification status. A document can be both Unclassified (not sensitive) and high integrity (verified and accurate) at the same time. These are independent security properties.
The Two Core Properties
Bell-LaPadula enforces confidentiality through two fundamental rules that control information flow. These properties work together to ensure that classified information remains protected from both unauthorized access and accidental leakage.
Simple Security Property (No Read Up)
The Simple Security Property is straightforward: you cannot read above your clearance level. Your clearance must be at or above the data's classification level. This is often called the "read down" rule because users can only read from sources at their level or lower—never above.
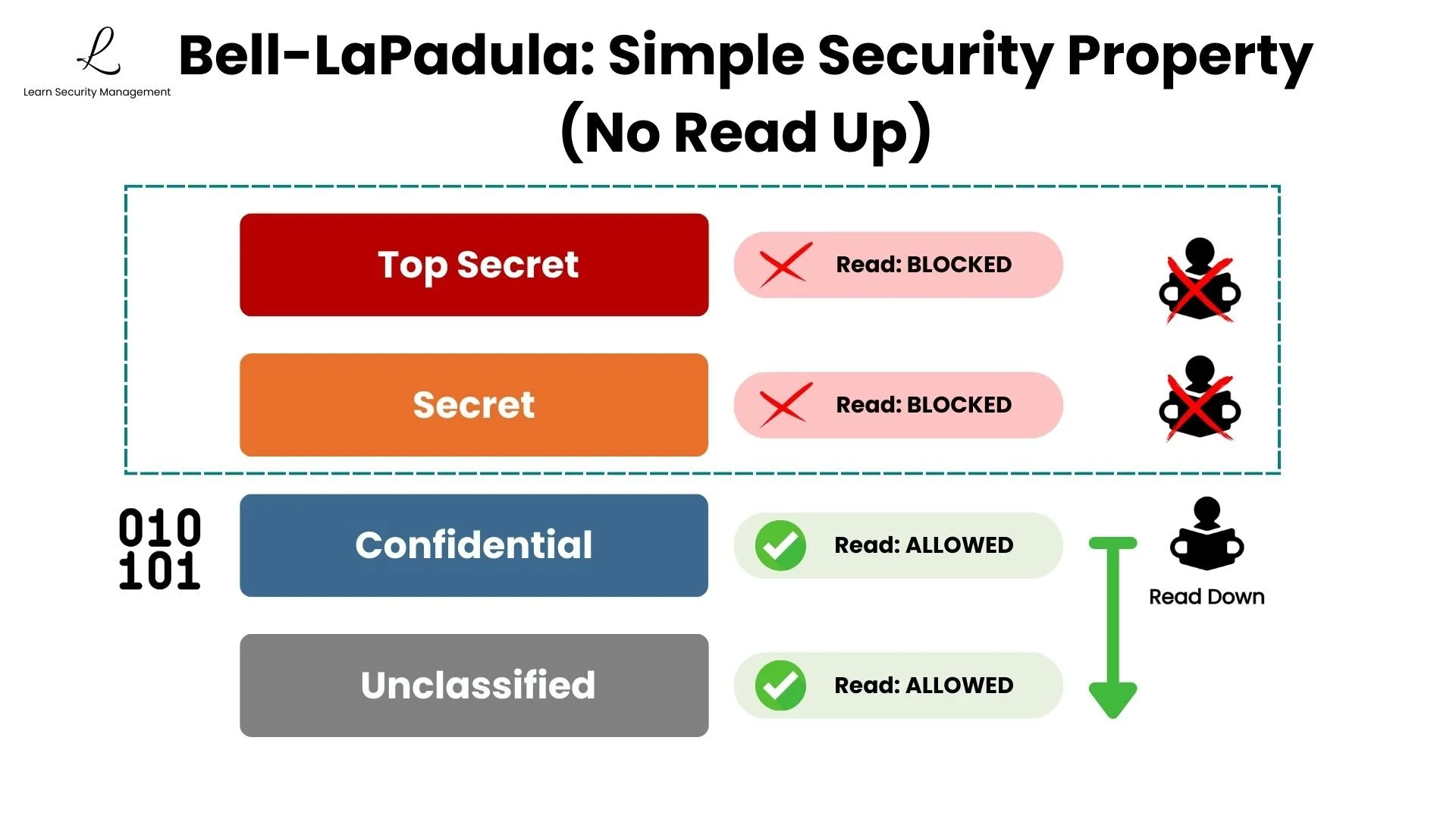
This creates an automatic barrier. Anything classified above your level becomes invisible to you—the system blocks access without requiring manual enforcement. You can read at your level or below, which is why it's also called the "read down" rule.
If you have Confidential clearance, Secret documents are completely invisible to you. You can access everything at your level and below—Confidential and Unclassified files—but the moment you try accessing something above your level, the system denies you instantly. This protects sensitive information based on need-to-know principles. A contractor with Confidential clearance might help analyze logistics data, but they shouldn't see Secret intelligence about ongoing operations. The rule protects sensitive information from people who haven't been cleared for that level of access.
Star Property (No Write Down)
The Star Property (*-Property) is less obvious but equally critical: you cannot write data to lower security levels. The data you write must be classified at or above your clearance level. This is often called the "write up" rule because users can only write to their current level or higher—never downward.
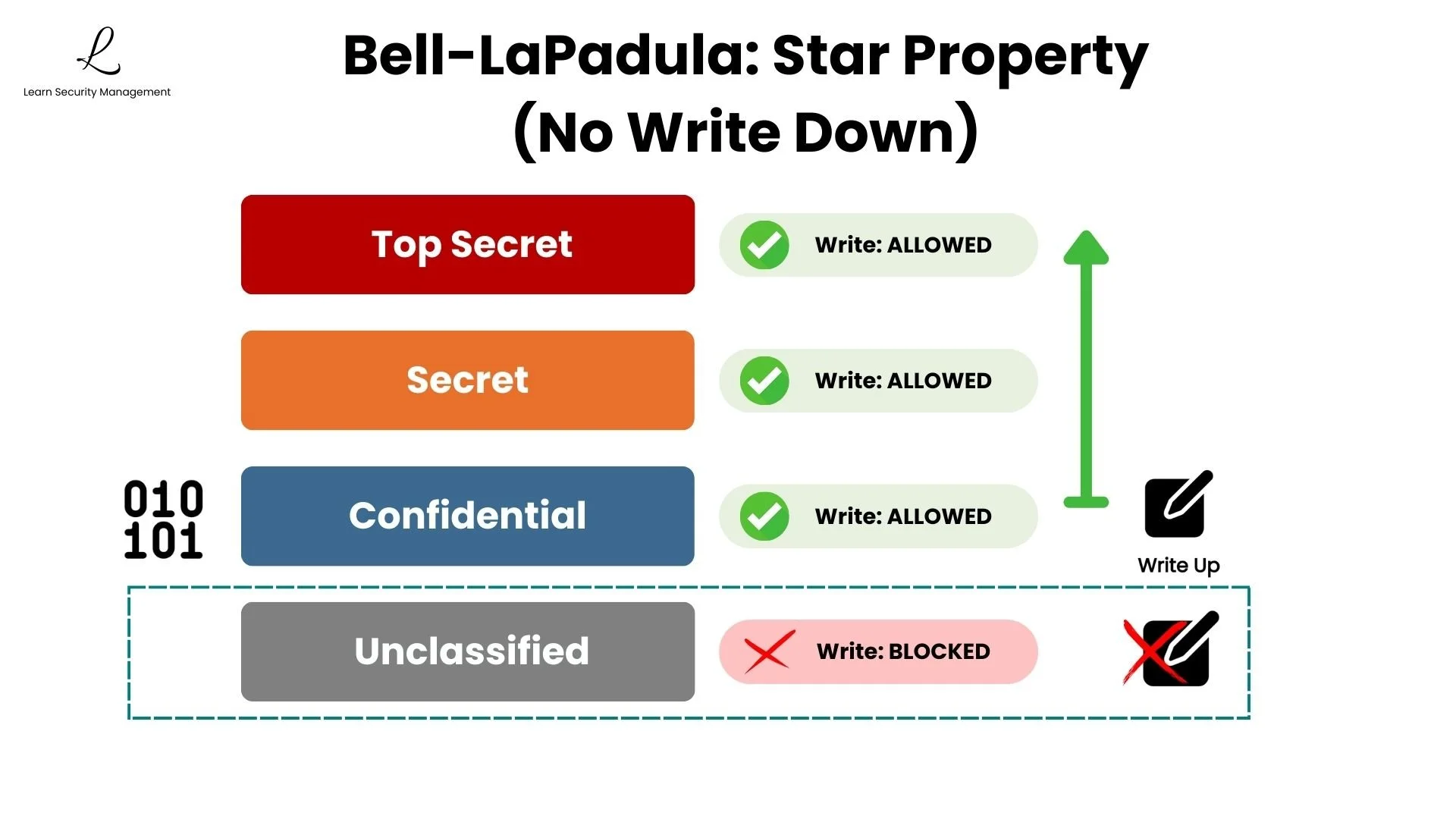
This enforces upward information flow. The system assumes your work contains sensitive information from everything you've accessed, so you must save it at your current level or higher. Data can only move upward in classification, which is why it's called the "write up" rule.
Imagine you're handling Top Secret intelligence—you now have access to classified information. If you saved your work to a Secret folder, that classified information would become available to users with only Secret clearance. The system forces you to write at your current level or higher, treating your output as potentially containing everything you've accessed. Once information enters a higher classification level, it can't flow back down.
Standard Star Property: Allows you to write to your level OR higher. Writing to a higher level is sometimes called a "blind write" because you can put data into a container you cannot see inside.
Strong Star Property: A stricter variation that restricts you to writing only to your exact same security level (no write up, no write down).
Remember the Bell-LaPadula rules by their opposites to Biba: Bell-LaPadula is "No Read Up, No Write Down" while Biba is "No Read Down, No Write Up." Both use the same structure but protect different properties—Bell-LaPadula protects confidentiality, Biba protects integrity.
Putting It Together: A Military Example
Let's see these rules in action. A security officer with Top Secret clearance is analyzing threat intelligence.
Reading (Simple Security Property): They can read documents at any level below theirs—Top Secret, Secret, Confidential, and Unclassified. The system grants them complete visibility of everything at or below their clearance level.
Writing (Star Property): When they write their assessment report, they must save it at Top Secret level or keep it at the highest classification they referenced. They cannot save it to a Secret folder, even though they have access to that level, because their report likely contains insights or details drawn from Top Secret sources. Saving it at a lower level would expose that classified information to users who only have Secret clearance, creating a leak.
- Reading: Information flows DOWN (you read from your level or lower)
- Writing: Information flows UP (you write to your level or higher)
- Protection: Classified data is protected from both unauthorized viewing (bad reads) and information leakage (bad writes)
Bell-LaPadula vs. Biba Model
Understanding Bell-LaPadula becomes clearer when you compare it to Biba, another fundamental security model. These two models are frequently tested together on the CISSP exam because they represent complementary but opposite approaches to access control.
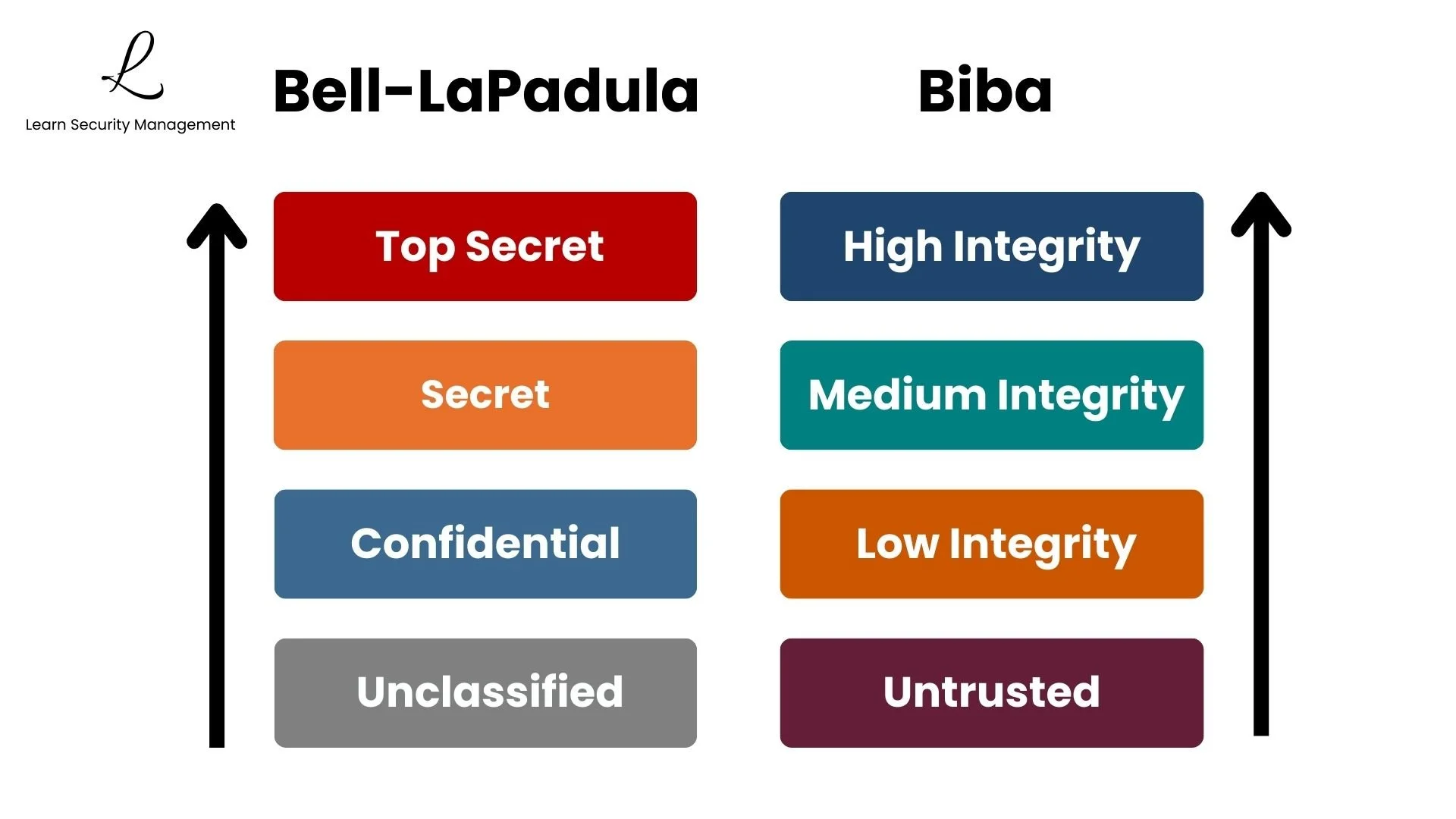
| Aspect | Bell-LaPadula Model | Biba Model |
|---|---|---|
| Primary Goal | Confidentiality | Integrity |
| Reading Rule | No Read Up (read down only) | No Read Down (read up only) |
| Writing Rule | No Write Down (write up only) | No Write Up (write down only) |
| Protects Against | Unauthorized disclosure of secrets | Data corruption from untrusted sources |
| Typical Use Cases | Military and classified systems | Financial systems, databases, medical records |
The Fundamental Difference
Bell-LaPadula is built around confidentiality—keeping secrets from unauthorized eyes. It uses No Read Up and No Write Down rules to prevent information leakage, making it ideal for military and classified environments. Biba, on the other hand, focuses on integrity—keeping data accurate and trustworthy. It uses No Read Down and No Write Up rules to prevent data corruption, making it perfect for financial systems where accuracy matters most.
Here's the fundamental difference: Bell-LaPadula treats higher levels as more sensitive and protects them from exposure. Biba treats higher levels as more trusted and protects them from corruption. One protects secrets from getting out, the other protects data from getting corrupted.
Contrasting Examples
Consider a military intelligence database using Bell-LaPadula. An analyst with Secret clearance cannot read Top Secret reports, and when they create documents, they cannot save them to Confidential folders. The system protects against espionage and unauthorized disclosure.
Now consider a bank's financial system using Biba. A bank employee processing transactions cannot read data from untrusted external sources that might contain errors, and they cannot modify high-integrity audit logs. The system protects against data corruption and maintains accuracy.
Bell-LaPadula protects against Espionage (stealing secrets, unauthorized viewing). Biba protects against Sabotage (altering data, planting errors, corrupting logs). Bell-LaPadula hides the data; Biba protects the truth.
Practical Limitations
While Bell-LaPadula is theoretically strong, it has limitations in real-world environments. Understanding these limitations is important for CISSP candidates and security professionals implementing access control systems.
| Limitation | Impact | Mitigation |
|---|---|---|
| No Integrity Protection | Authorized users could corrupt or delete data | Combine with Biba or other integrity controls |
| No Availability Protection | Does not prevent denial of service | Implement separate availability controls |
| Operational Bottlenecks | Data accumulates at higher levels | Declassification processes and trusted subjects |
| Classification Discipline | Requires strict security labeling | Automated classification and governance |
| Limited Collaboration | Cross-level work is restricted | Defined escalation and review paths |
Single-Focus Design
The model focuses only on confidentiality and ignores everything else. An authorized user could delete files, corrupt data, or crash the system—Bell-LaPadula wouldn't stop them because those aren't confidentiality violations. Organizations typically layer it with other models like Biba for integrity or implement additional controls for availability.
Data Flow Restrictions
The upward-only writing also creates a practical problem: Top Secret systems collect more and more data that can't move back down to lower levels, even when needed. This creates operational bottlenecks where information gets stuck at higher classification levels, requiring special declassification procedures to share with personnel at lower clearance levels.
The Bell-LaPadula Model provides no protection for integrity or availability—only confidentiality. For comprehensive security, organizations must implement multiple complementary controls. Never assume a single security model addresses all requirements.
Security models like Bell-LaPadula provide formal frameworks for specific security properties, but real-world implementations require layered controls addressing confidentiality, integrity, and availability together. No single model provides complete protection.
CISSP Official Study Guide, 9th Edition
Conclusion
The Bell-LaPadula Model provides a formal framework for protecting classified information through controlled information flow. By implementing the Simple Security Property (No Read Up) and Star Property (No Write Down), organizations can prevent unauthorized access to sensitive data and ensure that classified information cannot leak to lower security levels.
Understanding how Bell-LaPadula differs from integrity models like Biba is essential for CISSP candidates. While Biba protects data accuracy from corruption using opposite rules (No Read Down, No Write Up), Bell-LaPadula protects secrets from disclosure. These models complement each other in comprehensive security architectures.
For CISSP exam success, focus on understanding the two core properties and their practical applications. Remember that Bell-LaPadula addresses only confidentiality—organizations must implement additional controls for integrity and availability. When exam scenarios involve classified information, unauthorized access, or preventing disclosure, the Bell-LaPadula Model is your answer.
CISSP Practice Tests
Challenge yourself with tough, realistic CISSP scenarios that expose gaps before exam day does.
Take the ChallengeThe Bell-LaPadula Model is a security framework that protects data confidentiality by controlling information flow. It prevents unauthorized access to classified information and ensures that sensitive data cannot leak to lower security levels.
The Two Core Properties
- Simple Security Property (No Read Up): Users cannot read from higher classification levels—prevents unauthorized access to classified information
- Star Property (No Write Down): Users cannot write to lower classification levels—prevents classified information from leaking downward
Security Levels
- Top Secret: Highest sensitivity, grave national security impact
- Secret: High sensitivity, serious national security impact
- Confidential: Moderate sensitivity, damage to national security
- Unclassified: Public or non-sensitive information
Bell-LaPadula vs. Biba
Bell-LaPadula: Protects Confidentiality → No Read Up, No Write Down → "Higher = More Sensitive"
Biba: Protects Integrity → No Read Down, No Write Up → "Higher = More Trusted"
Key Limitations
- Single Focus: Only addresses confidentiality—no integrity or availability protection
- Operational Bottlenecks: Data accumulates at higher levels, requiring declassification processes
- Classification Burden: Requires strict discipline in assigning security levels
Common Exam Mistakes
- Confusing Bell-LaPadula rules with Biba rules (they are exact opposites)
- Assuming Bell-LaPadula provides integrity protection (it does not)
- Forgetting that security levels reflect sensitivity, not trustworthiness
- Overlooking that higher classification in Bell-LaPadula means more sensitive, not more trusted
The CISSP exam tests your understanding of security models as Static, Rule-Based frameworks. Bell-LaPadula is a confidentiality model that enforces fixed rules about information flow—it doesn't adapt based on context or user behavior.
1. Espionage vs. Sabotage
The exam frequently presents scenarios where you must identify the correct model based on the threat actor's goal:
- Espionage Scenario: A foreign intelligence agent attempts to access classified documents → Bell-LaPadula (protects confidentiality)
- Sabotage Scenario: A disgruntled employee attempts to corrupt financial records → Biba (protects integrity)
2. Understanding "Up" and "Down"
The exam may test whether you understand what "up" and "down" mean in each model:
- Bell-LaPadula (Sensitivity): "Up" = More Classified/Sensitive. Top Secret is "above" Secret.
- Biba (Integrity): "Up" = More Trusted/Verified. Audited financial data is "above" unverified input.
Keywords to watch for: "classified," "sensitive," "clearance," or "disclosure."
3. Practical "Manager" Takeaway
As a security manager, you use Bell-LaPadula concepts when designing data classification and access control policies:
- Security Clearances map to your employee background check and access approval process.
- Classification Levels map to your data labeling scheme (Public, Internal, Confidential, Restricted).
| Look for these Keywords | Think: Bell-LaPadula? |
|---|---|
| "Prevent unauthorized disclosure" | YES |
| "Classified information" or "clearance levels" | YES |
| "No Read Up, No Write Down" | YES |
| "Prevent data corruption" or "maintain accuracy" | NO (Biba) |
| "Military" or "government secrets" | YES |
Bottom Line: Bell-LaPadula is a one-way mirror—those with clearance can see in, but secrets never leak out. When the exam asks about protecting classified data from espionage, Bell-LaPadula is your answer.

